Network Packet Sniffers are an essential defense for modern networks. Welcome to our packet sniffer article! We hope to show you about the basics about how these apps work, why you need them, and where they can be used.
This is by no means a technical deep dive, but rather an introductory overview of what you could expect to do with a network sniffer.
There are TONS of different packet analyzer programs out there to choose from for inspecting massive traffic volumes down to a single packet, and we only looked at SolarWinds Network Performance Monitor in this article, but we plan on going through many, many more in the near future.
Let’s Learn: What is a Packet Sniffer in Networking?
Download a Free Trial of SolarWinds NPM
What Is A Packet Sniffer? We get asked this a lot because it doesn't exactly sound like a technical term to begin with. Well, computer networks are essentially a group of computers just communicating with each other. A packet analyzer or packet sniffer is the tool you can use in order for your computer (or any device connected on said network) to listen and watch all those messages going back-and into between devices.
What is a packet sniffer in networking? How are networks analyzed and what does a packet sniffer do? What are network packets and why are they sniffed? packet sniffer tool and packet sniffer android. Explain what is a packet sniffer and why you would use one.
A packet sniffer is a program that runs on your PC and captures all the packets passing through it. Packet analysis software such as WireShark, tcpdump or iftop can be used to analyze captured data in order for you to understand what traffic has been flowing over an interface; this may include passwords sent via email when browsing insecurely on a network or on the internet.
Packet sniffing is performed on a network to capture all the packets in an interface. This is useful for analyzing and checking data that has been sent over it, such as passwords or other sensitive information which may be transmitted insecurely on your wireless router at home; packet sniffing can also tell how much bandwidth you are using while browsing online if done through software like WireShark.
It has gotten much easier to run a packet sniffing analysis as a result of the rise in mobile devices and wireless networks; for example, you could use tcpdump or iftop on your Android device to check what traffic has been sent over it.
The following is just an excerpt from our article: What Is A Packet Sniffer And How Does It Benefit Your Network? Packet sniffer Android applications have matured in recent years, making them a viable tool for you to use when trying to analyze your own network.
Why Analyze your network with a Network Protocol Analyzer?
If you suspect a hardware or software issue with your network, then it is important that an analysis be conducted to determine what the cause may be. Network analyzers can also help diagnose wireless issues like interference and provide information on packet detection rates in order for them not only fix any underlying problems but improve their service as well!
There are plenty of other reasons that you might want to check what kinds of data are available on your network.
- Detect issues on your network: On a network of any size there can be unexpected issues that crop up. These can range from a bad configuration of the router or an outage with your ISP, to more serious issues like malicious software being spread on one end and not detected by other available security measures at either spot before it reaches its destination.
- Detecting these kinds of problems is important because they could ultimately lead you huge losses in productivity for both your users and customers. A packet sniffer helps to find out what the issues are, and what could be the cause.
- Alleviate network congestion: If there is a user or application that is spamming or flooding your network with packets, a packet sniffer can help to stop that. It does this by monitoring the network data for excessive or illegal activity and then reports back on what is happening.
- Alleviating these kinds of incidents will not only save you time from troubleshooting them but also provide better service quality it'll be unaffected too because other legitimate traffic won't be able to reach their respective destinations and that means that your network will be more reliable.
- Protection against viruses: One of the most common causes for a big company to lose productivity is due an attack by malware such as virus, trojan horse or worm on their critical systems and servers that might bring down IT operations throughout all departments in one fell swoop if they're not dealt with quickly enough
- Traffic Type Analysis: By using a packet sniffer you can determine the traffic type going through your network, which can help you analyze how much bandwidth is being used in certain areas and also if there's any need to upgrade or change a specific area of it.
- Network Monitoring: With firewalls on most networks nowadays its nearly impossible for anyone outside that particular company from accessing data inside their servers but when that does happen it is handy to have a packet sniffer available to run through the packet data. By doing this you will find the source of the attack and help to mitigate and then terminate it.
- Packet Analysis: A packet sniffer is perfect for analyzing packets, which can then be formatted into a readable report that identifies either issues with your network or security breaches This type of tool could also come in handy if you need any evidence collected before contacting law enforcement about some large-scale
A penetration tester uses a whole host of different tools to test the security of your network, and a packet sniffer is just one of many that they might use to see what traffic is being sent and received.
When analyzing your network, you can be alerted if any information has been accessed without permission or when a hacker could access sensitive data like passwords from the internal servers of an organization.
It is critical that you use packet sniffing software on networks that you have permission to access. Using packet sniffing software on a public network is not advised as you can potentially encroach on other people's privacy.
Getting Started With Packet Sniffing
To get started with packet sniffing you need to make sure that your network card run in the correct mode. This allows it to receive all data, even packets that it isn't necessarily supposed to receive. For the most accurate packet sniffing, you will need to turn on promiscuous mode.
A network card that is running in "promiscuous" or ``all-multicast`` modes can intercept packets from any other computer connected within your LAN - not just those it's intended for and also ensures traffic doesn't pass through a router. Once you have achieved this, then you can move onto some of the fundamentals of packet sniffing.
What is Omnipeek network protocol?
In order to conduct rapid network troubleshooting and diagnosis, Omnipeek decodes thousands of protocols. In addition to Ethernet, Gigabit, 10 Gigabit, 802.11a/b/g/n/ac wireless, and Voice over Internet Protocol (VoIP), Omnipeek Network Analyzer can also verify video to remote offices.
This packet analyzer software from Savvius, a company owned by LiveAction, helps with network troubleshooting and protocol analysis. A plugin API is available for better integration with existing systems and allows for development of customized solutions.
Packet Sniffing Fundamentals
In order to do any meaningful network data packet investigations you will need to capture data in transit on your network. The easiest way to do this is by using a packet sniffer, which can be installed as software or hardware and will enable you not only see all the traffic but also analyze it for potential security threats that could compromise both private computers connected within an office LAN environment.
Most modern packet sniffers have a lot of different graphical and visual tools to help you extrapolate useful data from the mountains of data that you will collect during the course of your packet sniffing investigations.
One of the most important data points that you will want to be able detect are ARP request and reply exchanges. Packet sniffing is also a good way for network administrators (or anyone with appropriate access) to see what services, applications or connections individual PCs on your local LAN use as they communicate over an Ethernet cable connection.
Be Selective in Your Data Acquisition
There is a lot of traffic even on the smallest networks, so you need to be selective in what data that the sniffer collects and stores.
You don't want your packet-sniffing tool collecting all of this incoming traffic (eavesdropping). So, for example if an Ethernet cable is connected between a PC at one location in your office or business with another similarly located computer which also has its network interface connected to the network then you might want to configure the sniffer rule for that specific connection only.
Try to think about the types of connections that you are concerned about, and create rules and filters that focus in on those targets first before you start collecting the traffic from all of your network connections.
If you are looking for a specific protocol then create an appropriate filter to capture those packets, or if it is content that matters more (e-mail messages) use filters based on keywords rather than trying indiscriminately collect everything in real time and sorting through later as this will be impossible to do while the data is in transit.
What are Network Packets?
Network packets are groups of data that contain all of the information that your various network systems need to communicate with each other. Each packet of data has information about where the data is from, who it is going to, and other data that will get it to the correct host.
Be Prepared for Encryption with your Packet Analyzer (Packet Capture Tool)
Sometimes the applications on your network will be using encryption to protect the data and traffic, which will make it very difficult for you to sniff. You will need to get creative when using a packet capture tool.
For example a user connecting with SSH (a secure shell application) over an encrypted connection is going to be immediately blocked by your firewall rules.
If this type or scenario exists then create separate filters that focus on these types connections first before trying to capture everything all at once. Remember that you want to collect actionable information that will help you to make a difference to your network and hopefully improve things as well.
If you are unsure about the protocols that your network is using, then it may be a good time to go back and review them before continuing forward with trying to capture all of the packets in hopes they have something useful for testing or debugging purposes at a later stage.
Can You Hack With A Packet Sniffer?
The short answer is yes, tech-savvy hackers can use a packet sniffer to access data that is not encrypted. However, there are some legal issues surrounding this type of activity so you should always consult with your lawyer before proceeding.
Another way that hackers can leverage the power of a packet sniffer to identify targets on a network . This is done by looking for outbound requests from the user's device that make it to a destination on the network.
A packet sniffer can be used as an excellent way of verifying whether or not your network has been compromised and should also provide you with clues about what type, so if there are any security loopholes present on other devices in its vicinity then you will find them with a packet sniffer.
Also, be aware it could create severe damage if the information they acquire has sensitive personal or company related details about employees on file. Data privacy laws are a big deal, so make sure that you respect them. Be sure that you have the correct permissions to legally use a packet sniffer before proceeding and always secure the data that is collected.
What Different Types of Packet Sniffing Tools?
There are plenty of different types of Packet Sniffing Tools, and there is a wide variety of different operating systems that support Packet Sniffing Tools. Examples of operating systems that support Packet Sniffing Tools includes Windows, Mac OS X, Android and Linux.
You must know the differences that Packet Filters and Packet Sniffers have from one another. Packet Filters are a type of packet sniffing tool that allows you to visualize network traffic as it enters or leaves your computer on an interface such as Ethernet card in order for specific packets to be filtered out from other data streams being transmitted over this particular segment.
Traditional Packet Inspection tools allow you to drill down into the packet details to see the packet payload and any header information that is attached to this particular data stream.
In a nutshell, Packet Filters act like an advanced level of network firewall where users can filter packets in various ways for testing purposes or troubleshooting reasons by specifying certain criteria such as blocking all IP traffic from outside your company's range while letting through only the permitted data types.
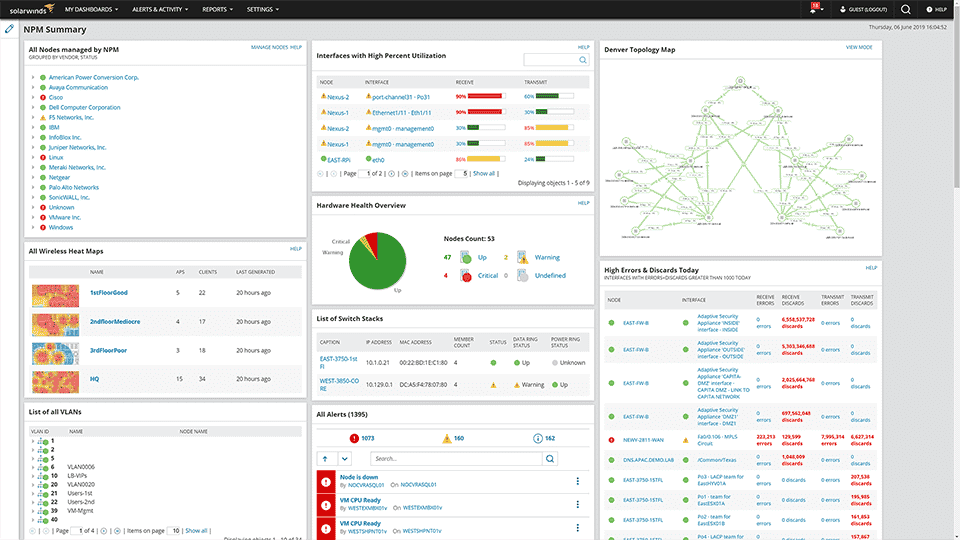
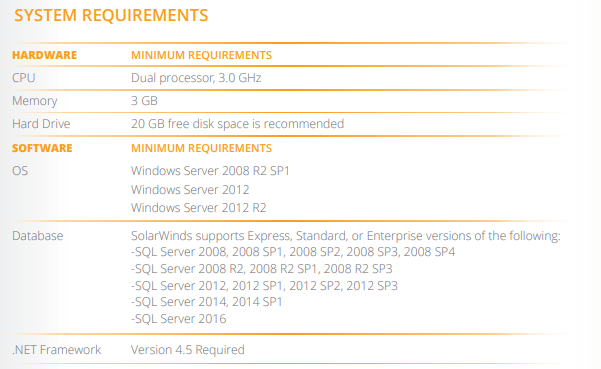
SolarWinds Network Performance Monitor
As far as Packet Sniffers Go, it is difficult to think of a more well rounded application that SolarWinds NPM.
SolarWinds NPM great all round monitoring and management system. It is a monitoring software application that provides 100% visibility into the performance of your entire IT infrastructure.
Our powerful agentless architecture delivers complete coverage for networks from end to edge with no gaps or blind spots so you know everything about what's happening on every single element of your network.
This is a great option for anyone who would like to monitor their network traffic and it monitors bandwidth, data usage as well. It also has overall monitoring capabilities of your entire IT infrastructure so that you are always informed on how everything is running.
SolarWinds Network Performance Monitor is a multi function tool that can also be used as a packet sniffer. It monitors bandwidth, internet traffic and data usage as well. It also has overall monitoring capabilities of your entire IT infrastructure so that you are always informed on how everything is running and can help identify issues wherever they are occurring on your network.
This makes it an especially useful application if you are concerned with how your network traffic is running and want the ability to see how everything is functioning.
NPM quick view of features and capabilities
- Troubleshooting, SLA impact and downtime.
- Advanced with critical path hop-by-hop analysis.
- Cross-stack data correlation for problem identification.
- Quick deployment with out-of-the box dashboards and alerts.
SolarWinds NPM Features
Monitor your network for performance, availability, and fault problems. Test your network with our packet sniffer tool.
Monitoring the performance, traffic, and configuration details of devices and applications in an on-premises environment.
Network data correlation is the process of analyzing multiple different pieces of information collected from various tools and then looking for patterns. In a packet sniffer, these logs are combined into one view to quickly make connections between events that otherwise wouldn’t be clear in time to find them on their own. Since network performance largely depends on underlying hardware.
You will be informed of issues on your network when and as they occur. Although no detailed information is provided about how the quality was rated, it's clear that the app works well enough as an effective tool to analyze network traffic.
An in-depth analysis of networking components is not easy, especially on your own. Scraping data from various connections with packet sniffer tools such as tcpdump are necessary when inspecting and analyzing networks for things like dynamic wired and wireless network discovery, performance metrics, link utilization, or coverage area between wireless devices.
Packet sniffer tool is used to find out where all of the network packets are going. It displays that information for you on a screen. Use a packet sniffer tool from F5 to monitor the health and performance of your devices. These tools can be used to capture network traffic.
In today’s wireless world, it is important to analyze wireless networks in order to ensure flawless performance. Packet sniffers allow you to capture and view data transmitted between a managed device and its corresponding access point or controller.
Monitoring network infrastructure is more affordable and automated. The solution has off-the-shelf monitors, alerts and reports that can help adjust your technology to meet changing needs.
Network monitoring software allows you to monitor and troubleshoot networks from a single program. It also provides accurate data about network performance, including packet captures, which can be used for forensic analysis of specific events such as threats or potential attacks.
A packet sniffer is a software application that allows software engineers or network administrators to scan the traffic passing between two computer systems at close range so they can monitor and/or modify activity on the networks.
Network packet analysis is the examination of packets allowed into and leaving a network for any changes in application end-user experience or causes.Color-coded graphs that show network and device performance. Track network performance with packet sniffers.
Time to Wrap Up
Now that we know what packet sniffing is, and why you would want to use a product like SolarWinds to do it with, it's time to wrap up and see what we have learned.
We hope that this article has provided you with a little bit of the necessary knowledge and background information about packet sniffing, including what it is used for in networking scenarios as well some of its benefits that can help networks run more smoothly.
If you want to try it out for yourself then be sure to download a free trial version here, and check this link for more information.
You can check out our shoot out article where we covered some basics about some traceroute tools, and also some interesting VPN and PowerShell content all in our blog section.
SolarWinds NPM Pricing
Download a Free Trial od SolarWinds NPM
Download a Free Trial od SolarWinds NPM