What is SSH?
Secure Shell (SSH) is a network protocol that enables users to access their computer over an unsecured network. SSH stands for Secure Shell too. This protocol provides strong password authentication and public key authentication.
There is also encrypted data communications between two computers connecting on the internet using an SSH key. SSH is used by system administrators because it provides strong encryption, which is important to them.
SSH Software
SSH has proven to be very useful for remote workers thanks to its impressive security thanks to key management.
A protocol that is both "Secure Shell" and a suite of utilities to implement it. It uses the client-server model.
It connects a Secure Shell client application, which is the end where the session will be displayed, with an SSH server, which is the end where the session runs.
The SSH implementation often includes support for application protocols used in terminal emulation or file transfers.
The protocol can also be used to create secure tunnels for other application protocols such as X Window System graphical sessions remotely.
SSH Meaning
In simple terms, SSH is about security. SSH is a computer program that manages files and shows them on the screen. It is used in many places, including schools and offices.
The SSH protocol is a tool that manages and secures the connection between two computer systems, transferring information in both directions.
It can be used to create secure tunnels for other application protocols such as X Window System graphical sessions remotely.
This protocol often includes support for application protocols used in terminal emulation or file transfers (such as Telnet or Rlogin).
SSH History
In the year 1995, Tatu Ylönen, a researcher at Helsinki University of Technology in Finland, created SSH. This was because there were people who could sniff passwords at the university.
SSH replaced older protocols that did not have strong authentication or privacy. In July 1995, he released it to 20 thousand users in fifty countries and SSH quickly became popular.
In 1995, Ylönen founded SSH Communications Security to market and develop software called SSH.
The original version of SSH used pieces of free software, but later versions released by SSH evolved into more proprietary software. By 2000, it is estimated that there were 2 million users using SSH software.
In 1998, a bug was found in SSH 1.5 that allowed hackers to insert content into an encrypted connection. A fix was made to SSH and most implementations had it.
However there was another bug in these SSH implementations that allowed people to do something with the computer's power (give themselves access).
In November 2008, a problem was found with SSH. It was for all versions of SSH. It let people see parts of data that should have been hidden.
One solution is to use CTR instead of CBC mode. This makes it so that anyone cannot see the data in this way now because the problem has been solved and no one can do this anymore.
How does SSH work?
Secure Shell (SSH server and SSH client) is a way to make sure that you can log in to other computers. Sometimes people think it's hard to find the right password or they don't know what to do on the computer.
Secure Shell makes it easy. You can also use Secure Shell for transferring files from your computer to another one, like when you want someone else to have something that you made and put it on their computer for them.
The computers talk to each other by using a public key. This helps make sure that the computers are who they say they are. Each computer has its own private key and a public one.
To start talking with a remote machine, the machine creates a new public key and uses it to send something encrypted to the other computer where it will decrypt and show you what was sent from SSH clients.
Where can I use SSH?
SSH is a way to connect with the servers in a data center. It was used to create secure connections to different types of resources, and for managing different types of things.
SSH can be used with many other things like routers and server hardware with the SSH protocol. You can also use SSH file transfer to remote systems and additionaloperations by using a secure SSH key.
Secure Shell is a type of program that helps connect to servers. It can let you make changes, perform uploads and exit. You can also use it with tools or directly through the terminal on a computer.
Sometimes, SSH keys are used to automate access to servers and they often work in scripts, backup systems and configuration management tools.
They provide single sign-on (SSO) so that people do not need to type their password each time they want to move between their accounts on the computer.
The SSH protocol is used to connect to a computer and to keep your information private.
SSH does more than just allow you to use it with the user ID and password that you have. Instead, SSH uses public key pairs in order to make sure that the computers are talking with each other through an encrypted connection.
In order for you to use it, you need your user ID and password (or other authentication methods) so that the computer knows who you are.
SSH Commands
You can use SSH commands to change the way you connect to a remote machine or a remote host. It is supported on multiple operating systems, not just Linux.
These are usually done at the command line with SSH, but you can also do them in a script.
The most basic form of SSH command is to invoke the program and destination host name or IP address:
ssh server.itblogpros.com
This will connect to server.itblogpros.com in order to create a secure connection over TCP using port 22 for the default SSH protocol, or changing these parameters if you need more security.
SSH commands are widely available and can be used for many purposes, such as connecting to a remote computer.
If you are a Linux or Unix user, these commands will allow you to do things like:
- Use SSH for connecting through an alternate port (e.g., ssh -p 2400 server)
- Use SSH for setting up remote command execution with one command line
- Connect to a remote machine or remote host with SSH from your local machine and execute SSH commands remotely
- Securely copy files over an ssh connection.
- If you are using Windows, then there are many options below for you to choose from
As you can see from the examples above, SSH is used to connect to a remote machine or a remote host securely from your local machine.
This is very important for remote workers that need to complete secure file transfer operations to a remote machine while using SSH.
Remote host functionality is very important when using SSH, which explains why it has become so popular since the beginning of 2020.
What are some SSH alternatives?
The SSH protocol is one way to run your applications securely over the network. SSH itself is a powerful tool that enables remote access and file transfers over an encrypted network.
There are many ssh commands that you can use when running it from a command line, making it highly useful and flexible.
If you're looking for the best ssh client to meet your needs, it's important to take into account which features are most important to you.
This article will explore five of the top-rated ssh clients on the market today, each with its own benefits and drawbacks in terms of cost, ease-of-use, compatibility with other operating systems and security protocols.
We have chosen a wide variety of apps that can run on multiple operating systems.
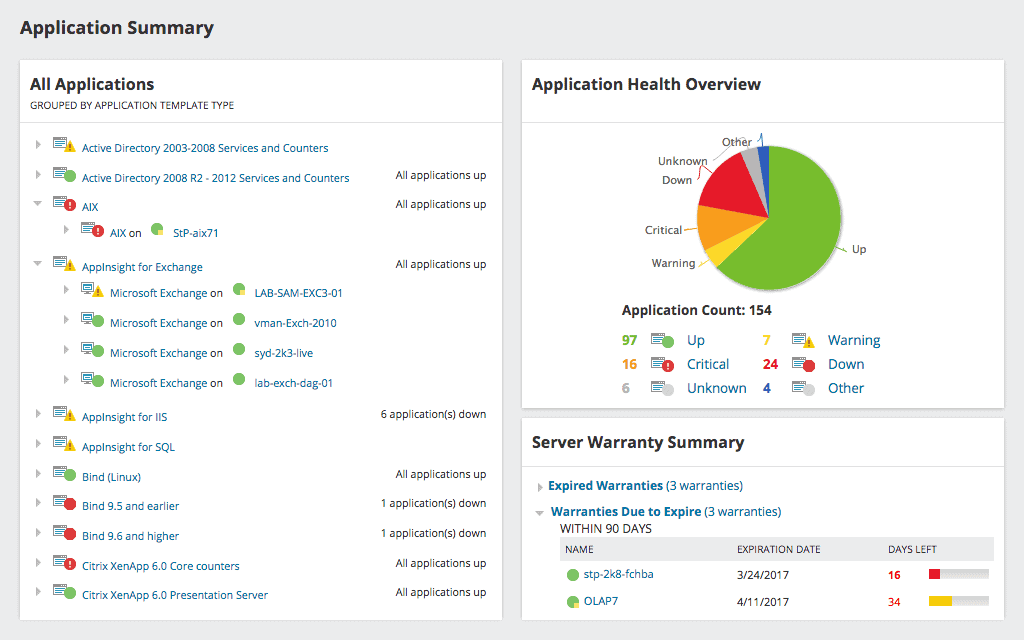
- Solar-PuTTY: Solar-PuTTY is a free and open source tabbed SSH client for Windows. It allows you to manage multiple sessions from one console, save credentials or private keys to any session for easy login, automate all scripts you're using when connection is established and find your saved session easily thanks to Windows Search integration.
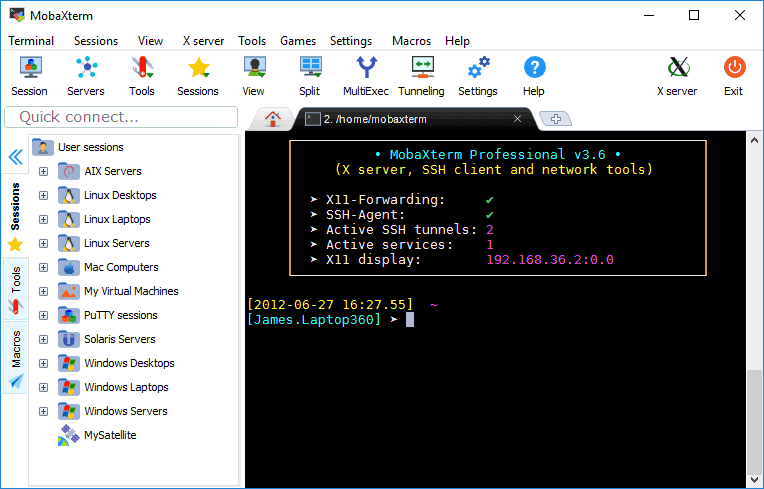
- MobaXterm: Login to a remote server from your computer using MobaXterm! You can choose any type of session you want. Every time you initiate a new connection, the application automatically saves it for later use and displays in left sidebar system tray icon. When logging on with SSH, SFTP browser pops up displaying all files available for drag-and-drop transfer directly into local Windows PC applications through secure connections over an encrypted network channel.
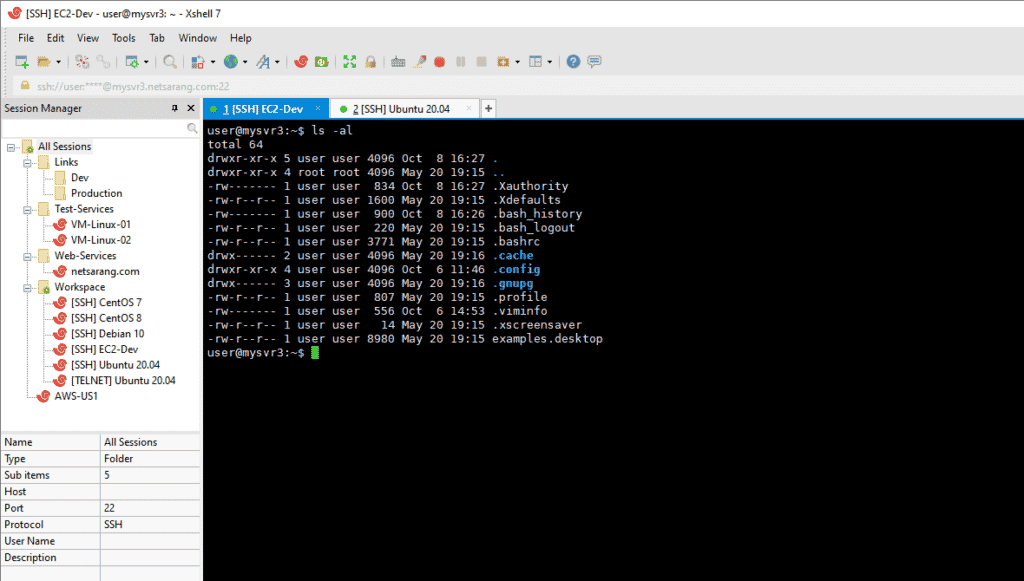
- mRemoteNG: mRemoteNG is a fork of mRemote, an open source remote connections manager for Windows that has seen many improvements and new features added. It allows you to view all your remote connections in a simple yet powerful tabbed interface where any connection can be started or stopped with the click on its icon; settings are also easily accessible through right-clicking. The list includes RDP (remote desktop/terminal server), VNC, ICA(citrix independent computing architecture) ,SSH (secure shell), and telnet.
- Xshell 6: A highly-rated SSH and telnet client that supports a variety of protocols, including SFTP (secure FTP), TELNET, RLOGIN and SERIAL. The program includes multi tabs in a single window as well as the ability to display multiple tab groups in one window for easy management; this is particularly helpful when working with servers where many jobs need completion simultaneously. Users can also set up their own key mapping schemes using VB scripting or Python scripts which are powerful alternatives to traditional terminal applications like PuTTY or SecureCRT. In addition it features IPv6 support so users will never be slowed down by an IP address shortage again.
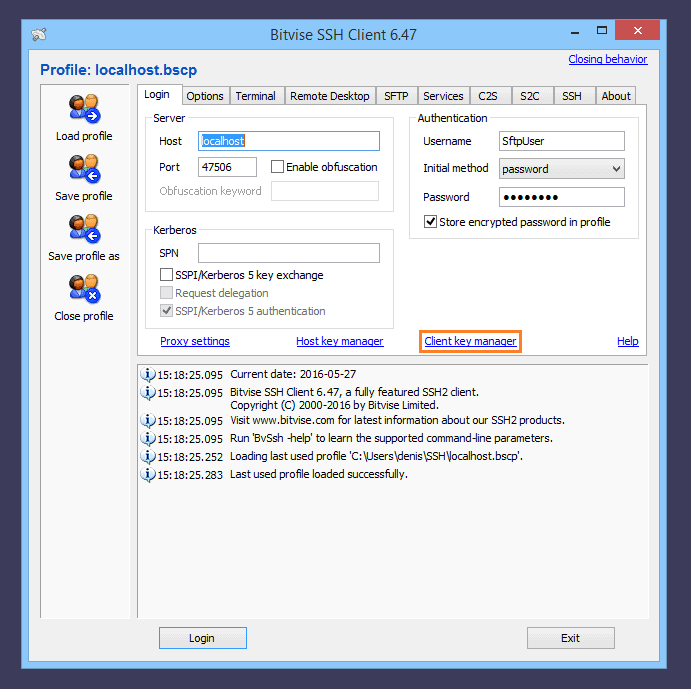
- Bitvise SSH Client: Bitvise SSH Client is a free file transfer, terminal and tunneling software for Windows. The client supports all desktop versions of Windows as well as Microsoft's server version from XP SP3 to the most recent – 10 and 2019 editions on both 32-bit (x86) and 64-bit architectures (amd64). For an enterprise or organization users, Bitvise’s SFTP clients are offered at no cost with support for unlimited concurrent sessions in several simultaneous instances that can be configured by administrators. Moreover, there are features such as one click remote access forwarding which makes it easy to extend your workstation onto any other device you have management control over while ensuring encryption keys remain safe during transit.
What is Data Encryption?
If you want to keep your data private, you can encrypt it. This turns the data into an unreadable format so people can't steal it. There are different types of encryption like SSL and TLS or TOR and VPNs. You need to make sure that the type of encryption that you use will give you the security that you need!
Protecting data is important. Data is more likely to be stolen online. The most common types of encryption are AES, RSA, and DES.
People use encryption to keep the data safe like when they have transactions on their bank account and don't want it to be stolen by someone else who has access on the internet.
What are the different types of encryption?
There are many different types of encryption. There is SSL, which is used to protect your personal information on certain websites when you're banking or shopping online, and TLS which is used for securing data from other sources.
Other examples of security measures that are available include TOR, VPNs, and Cloudflare DDoS protection.
Conclusion
You might already be familiar with Secure Shell (SSH) because it is commonly used in many industries, although many people might not know that they are already using it via an SSH client.
It can be used on a local machine to connect to a remote computer.
It’s a network protocol that enables users to access their computer over an unsecured network, and also provides strong password authentication and public key authentication.
System administrators use this protocol for its encryption abilities which are important to them when accessing servers remotely on the internet from anywhere in the world. This is very important for remote workers.
We hope you have found this article useful, and that you have learned about some SSH alternatives for connecting to your remote site or remote computer.
Try out SolarWinds SolarPutty
If you aren't using SSH yet, try out SolarPutty! Follow the download link below for more information about how it can help your business succeed at remote administration tasks while keeping all of your data encrypted end-to-end without any third party interception possible.